#
Tag: video
See all tags.
Below is info from a really old internal doc I kept at one of my past jobs, but it gave our customers some ideas for traffic they might want to filter on their egress Internet connection to keep potentially bad stuff away.
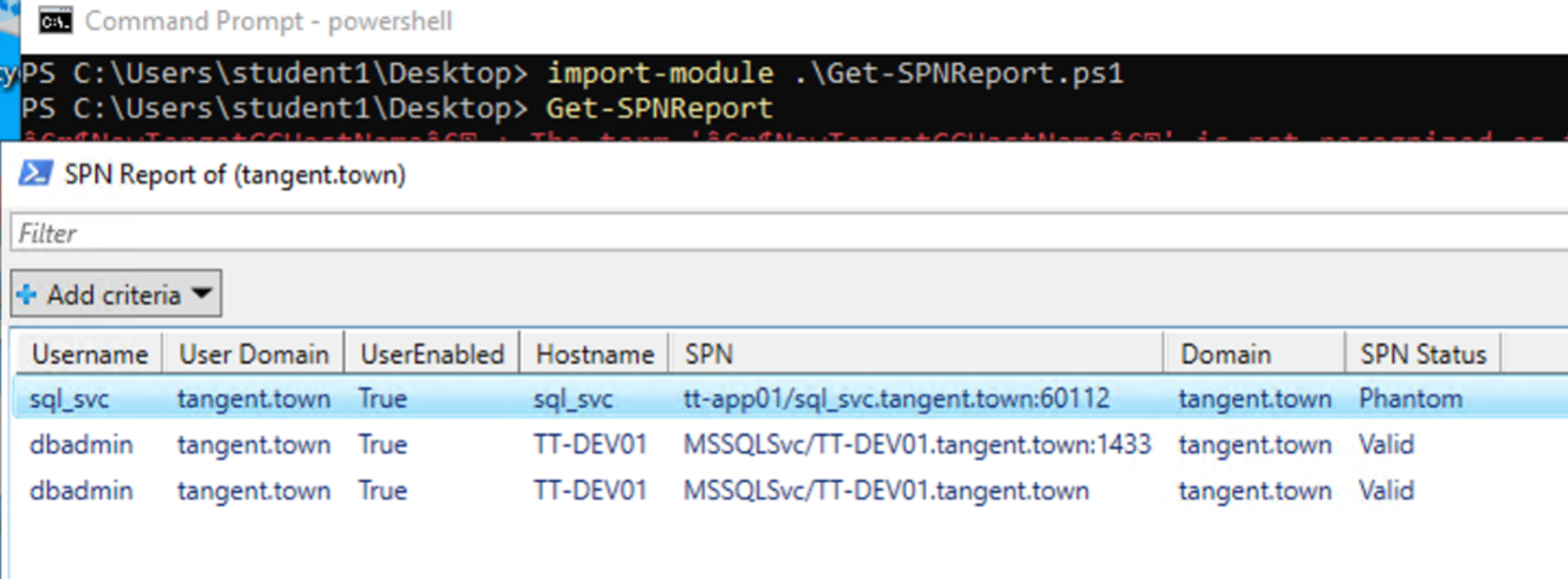
_wald0 has a helpful tweet on preventing Kerberoasting. Also, this article from MS shares "a practical way to clean up dead SPNs in Active Directory," and authored a script to help in the cleanup efforts as well.
Local Administrator Password Solution (LAPS) "is a Windows feature that automatically manages and backs up the password of a local administrator account on your Microsoft Entra joined or Windows Server Active Directory-joined devices. You also can use Windows LAPS to automatically manage and back up the Directory Services Restore Mode (DSRM) account password on your Windows Server Active Directory domain controllers. An authorized administrator can retrieve the DSRM password and use it."
A 7MinSec customer reported this was an effective way to remove the ability for attackers to play games with stored procedures:
Right now the best source I have for this is the pentest dropbox episodes for the 7 Minute Security podcast. I'll start moving over cmd-line snippets and
I'm in the market for a new USB wifi pentest adapter (TLDR: I really like the Panda PAU09 N600), and these resources helped me zero-in on good options:
An awesome tool for abusing ADCS. Check out the awesome accompanying wiki for attack syntax.
An awesome tool designed "with the single purpose to obtain machine-in-the-middle positions combining the techniques of mitm6 and only the name resolution spoofing portion of Responder." (source: Pretender GitHub and blog). We also covered this tool a bit on one of our Tuesday TOOLSday episodes.
A cool password filter to stop people from picking weak passwords in AD!